Cybercrime is a problem for all internet-based businesses, though each industry has its own threats, risks, and weaknesses. That said, it’s unsurprising that ecommerce businesses are some of the most at-risk because they deal with transactions and sensitive personal data. Data analysts at Zippia summarized that cyber-attacks happen every 39 seconds, 95% result from human error, and cybercrime cost Americans $6.9 billion in 2021.
Unfortunately, companies that have quickly expanded into ecommerce can overlook cyber security, putting them at greater risk than most businesses. The key lesson is that the more challenging ecommerce companies make it for cybercriminals to barge in and steal from them, the more likely they are to give up and move on.
In this article, we’ll show you how to keep cybercriminals away, examine how cybercrime affects ecommerce, and discuss some common attacks to look out for so you can avoid them.
5 Ways Ecommerce Sellers Can Prevent Cybercrime
Use these five strategies to reduce your business’s exposure to cybercrime. Here’s how to protect yourself from cybercrime.
1. Use Longer Passwords with MFA (Multi-Factor Authentication)
It may seem obvious to some, but plenty of people still have embarrassingly weak passwords. But there’s more to strong passwords than you may know. In addition to adding a combination of numbers, letters, and special characters, you want to avoid easily guessable passwords and patterns, as they’re easier for hackers to crack.
If you didn’t already know, password length does matter! A password of six characters can be hacked in as little as eight seconds, while a password of 10 can take up to 21 years. Alex Weinert, Director of Identity Security at Microsoft, explains that “each additional character takes 96 times longer” to decipher by a machine. This is because each additional character adds thousands more possible password variations. Weinert recommends using a password of at least 12 characters that has never been used before, though you usually need a password generator for this.
You also want to avoid using passwords that have appeared in past data breaches. You can check this using services like Pwned Passwords, which will tell you if the password you have been using has appeared in a data breach. If it appears, you should change your password immediately. It doesn’t mean that you have been hacked or that any of your data is freely available, but the fact that that password has appeared in breaches suggests that hackers may reuse it.
Multi-factor authentication (MFA) also makes a massive difference. It keeps your accounts way safer than just using a password, which machines can figure out. Weinert adds, “Based on our studies, your account is more than 99.9% less likely to be compromised if you use MFA.” So, if you’re not using MFA yet, get on it now.
Lastly, you can use mobile authenticators, similar to MFA—you log in with your credentials, then use an authentication app on your phone to generate a code and enter that into your device. Google and Microsoft both offer authenticator apps.
2. Teach Employees How to Spot Cyber Scams (And to Be Careful With Sensitive Data)
Employees can make mistakes when not adequately trained on security and avoiding scams, which can be costly. They can easily fall for phishing scams, such as those asking for sensitive data from someone pretending to be one of your partners.
According to Verizon’s cybercrime statistics, 30% of data breaches involved ‘internal actors.’ Verizon explains that this is not so much that all employees are ‘bad actors’ but more so that they can make mistakes that can accidentally share sensitive information.
The lesson here is to have rules and best practices for sharing company data and to invest time in training your employees. It’s important to teach your employees to question why someone is asking them to do something and to escalate the situation if they are unsure.
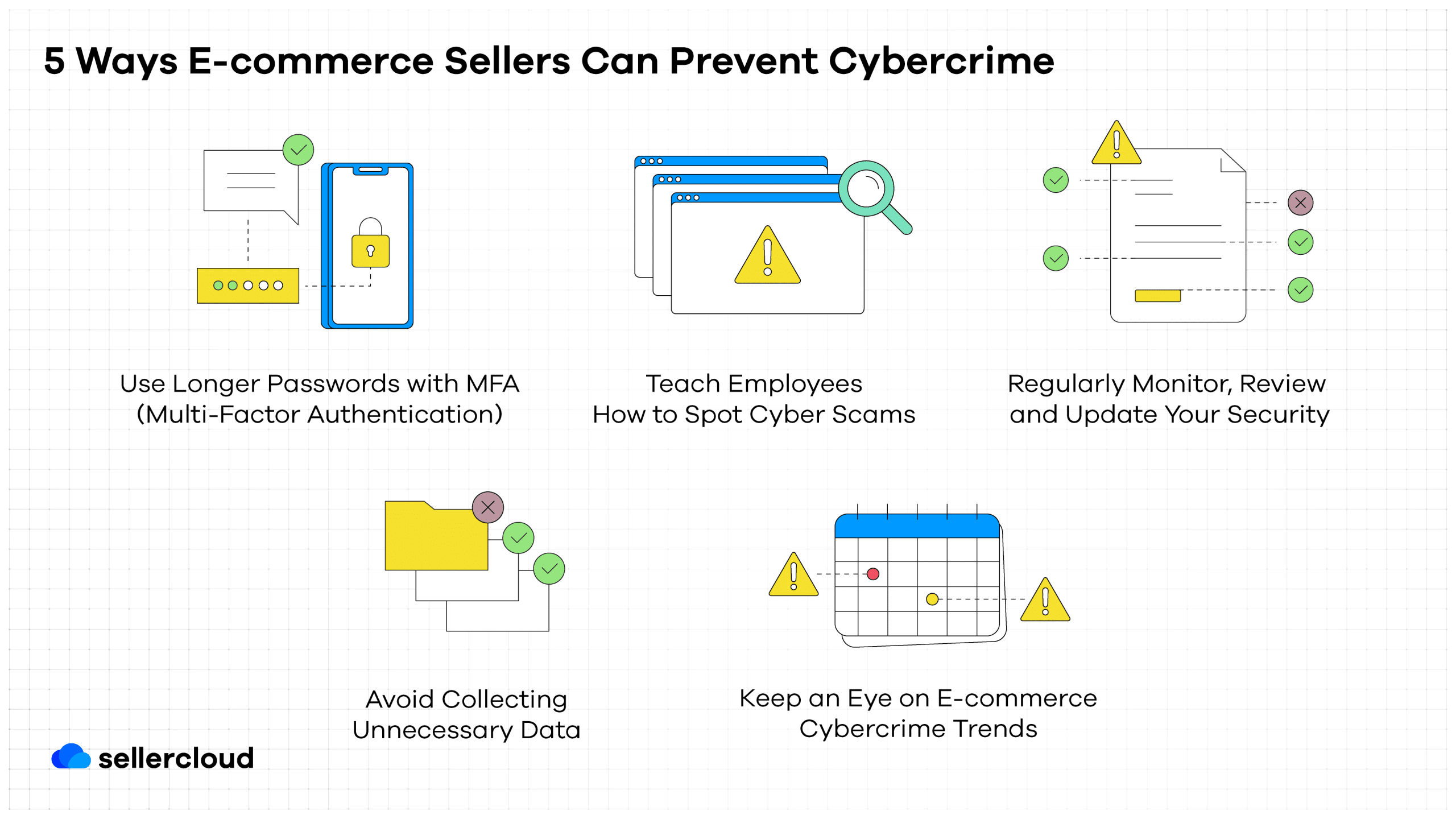 3. Regularly Monitor, Review, and Update Your Security
3. Regularly Monitor, Review, and Update Your Security
If you’re not doing this already, start now. During the pandemic, many retailers rushed into ecommerce, which meant security was sacrificed to get online quickly. When it comes to keeping your tech secure, there are quite a few risks and things to look out for, so it’s essential to test and patch vulnerabilities continuously. You don’t want cybercriminals locating weaknesses before you do.
Another risk comes from using many third-party tools in your ecommerce service. Hackers can find a vulnerability in some of your company’s services and use that as a backdoor. For example, sellers who use WordPress may be using outdated plugins that have become vulnerable to hackers.
Always monitor your tools and any updates. Some tools can do this for you. You should also look for release notes, particularly if they recommend an update for security reasons. You should adopt the latest industry-standard tech, such as a malware scanner, and use an ecommerce platform with built-in security features and SSL encryption.
The final point is to give your IT team time to focus on technical debt! Listen to them if they say something is important for security and must be fixed. Never underestimate the importance of sealing off entry points for cybercriminals.
4. Avoid Collecting Unnecessary Data (And Get Rid of It When You Can)
Customer data is useful for ecommerce businesses because we can learn from our consumers and improve online shopping experiences. However, it’s also highly risky to collect, and sellers are responsible for protecting this data. According to IBM Security’s “Cost of a Data Breach Report 2020,” 80% of breaches included customer PII (Personally Identifiable Information).
Of that data, emails and credit card information are often primary targets for cybercriminals. In an article for TotalRetail, Mark Whitehead adds that 53% of cyberattacks on ecommerce seek to steal ‘card-not-present’ (CNP) data. To reduce the fallout from a data breach, ecommerce companies should be selective about the customer data they collect and avoid collecting customer PII that they’ll never need.
Hackers can use PII to access customers’ finances and enable them to engage in other malicious activities, and the more PII they have, the easier it is for them. If that wasn’t enough reason to remove unnecessary PII, Varonis’s 2018 Global Data Risk Report states that “54% of data is stale,” meaning it’s no longer usable.
5. Keep an Eye on Ecommerce Cybercrime Trends
Security should be at the forefront of your mind and always be a part of your future ecommerce plans. The only way to do this is to keep a watchful eye on cybercrime trends. Ecommerce is constantly evolving, which means cybercriminals must continuously adapt to change. Quite often, technology changes and ends one tactic, but another is always around the corner. When one door closes, another one opens.
So, when adopting something new in your ecommerce business, you should first consider the potential vulnerabilities and how to avoid them. This also means watching out for when your partners and integrations are hacked and preparing for such a scenario.
How Does Cybercrime Impact Ecommerce?
Cybercrime can wreak enormous damage on ecommerce companies. If data is stolen or leaked, it can damage a company’s reputation and negatively impact sales. A research paper by Mansoura University on the impacts of cybercrime on ecommerce notes that it comes down to ‘trust.’ They explain that cybercrime can be one of the top reasons buyers avoid ecommerce and that when a store or platform is attacked, they can often take their business elsewhere.
So, it’s vital to ensure their safety and make buyers feel safe to return to you. Sometimes, it can take companies years to regain that trust after an attack. Data breaches are also extensively time-consuming to deal with and perhaps more expensive than you’d think. IBM Security’s Cost of a Data Breach Report 2020 says that a company can take up to 207 days to identify a data breach and, on average, another 73 days to contain it.
This means a data leak can be a massive headache for a long time. You may be dealing with the fallout from a data breach for well over a year. IBM Security also added that the average total cost of a data breach in 2020 was approximately $3.86 million, a 10% increase since 2014. Furthermore, there are costs associated with patching up vulnerabilities, and you may need to pay compensation to customers, and your company could even be litigated.
3 Famous Cybercrime Cases and What We Can Learn From Them
If we haven’t scared you enough yet into taking precautions to protect your ecommerce operations from cybercrime, we found some horror stories to share with you as a reminder.
eBay May Have Forgotten About MFA
In 2014, eBay’s corporate network was hacked, and information on 145 million customers was stolen. The hackers used multiple techniques, but eBay’s biggest fault was supposedly not using MFA. The same year, eBay lowered sales projections by $200 million due to the breach.
Carousell Didn’t Detect a Hack for Five Months
In 2022, Carousell, a highly popular Singaporean ecommerce platform, was hacked, and the emails and phone numbers of approximately 1.95 million users were leaked. And if this wasn’t bad enough, Carousell was only made aware in October 2022, and the hackers claimed the hack took place in May, meaning it was undetected for five months.
Amazon Always Has a Target on Their Backs
As the largest ecommerce platform, it is perhaps unsurprising that Amazon has been attacked by cybercriminals a lot. Amazon has been hacked so often that Michael X. Heiligenstein of Firewall Times wrote a full timeline of Amazon attacks up until 2022.
However, Amazon has been smart enough to work with hackers instead of against them, paying out bounties to hackers for finding security vulnerabilities. According to Forbes, in 2021, Amazon paid out $832,135 to hackers in a live hacking event for identifying vulnerabilities.
Common Cyber Attacks on Ecommerce Sellers
Ecommerce sellers can expect a plethora of different attacks, though cybercriminals can be creative and add their own twist to make them less detectable. According to an article by Brad Liggett of TotalRetail, there are two primary cybercrime trends in ecommerce in 2023.
The first is ‘refunding,’ where scammers attempt to get refunds for products they didn’t buy, often exploring loopholes or attempting to emotionally manipulate customer support. The biggest platforms are often the most common targets for this scam—Amazon, Apple, Target, and eBay. Typically, scammers will claim that a product never arrived, the box was empty, or they received the wrong item. In a blog post, we recently covered how to prevent such scams.
The second trend is phishing, which has been around for decades. Typically, a buyer receives an email saying their order is on the way (though they didn’t order anything), and they click on a link asking them to log in on a fake landing page. Doing this gives the scammers the customer’s login details, which they can use to enter their account.
Liggett notes that investing in security tools won’t necessarily keep you safe from phishing. Often, mitigating phishing comes down to knowing cybercriminals’ tactics. One of the easiest ways to spot such email scams is unusual email addresses and spelling errors. Phishing will likely continue to be a problem for sellers and consumers and will keep evolving.
According to an article by Velvet-Belle Templeman of Digital Nation, ecommerce fraud is expected to exceed $48 billion globally in 2023, up 16% from $41 billion in 2022. This potential increase is tied to the risks associated with the rise of digital wallets and buy now, pay later (BNPL).
Book a free demo today to learn how Descartes Sellercloud can help you better manage your ecommerce operations.





